Event log and security debug
Event log
The Event log application is a place in the administration interface where the system records events and activities. From a security point of view, the events logged into the event log are mainly:
- Authentication attempts – both successful and failed
- All bad requests – which includes attempts of SQL injections and other hacking efforts
You can find more information about event log settings in Working with the system event log.
Security debug
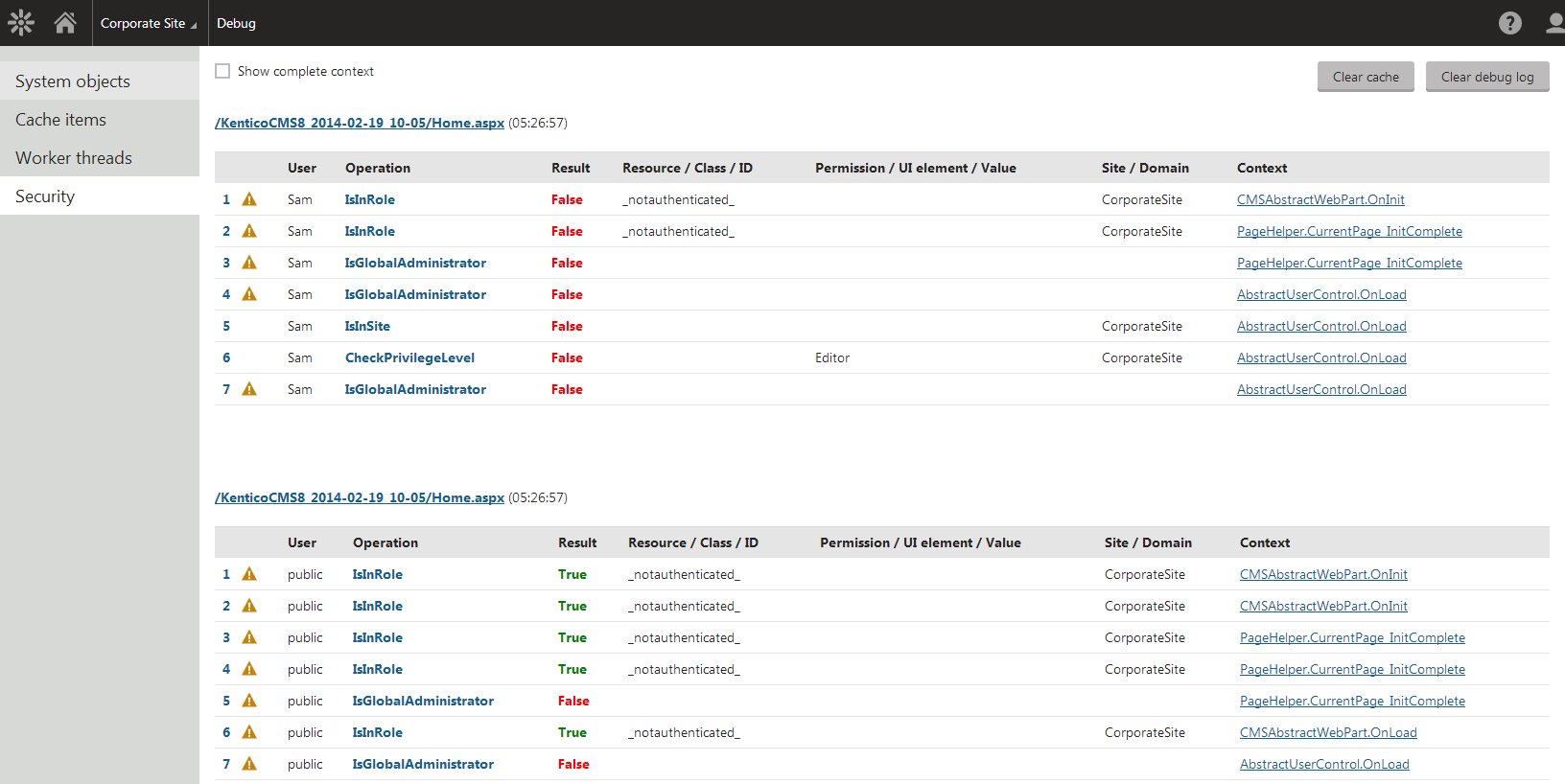
The security debug is a part of the debugging interface in Kentico. You can find the security debug interface in the Debug application on the Security tab.
Enabling the security debug
If you cannot see the Security tab, you need to enable the security debug in Settings -> System -> Debug by selecting the Enable security debug option.
The security debug allows you to view user security checks performed by the system. Information stored in this section includes:
- IsGlobalAdministrator, IsEditor, IsInRole, IsInSite, IsCultureAllowed and IsGroupAdministrator checks
- URL and macro signature hash validation
- redirects to the AccessDenied page – for missing permissions and UI element access